由于大规模使用Kuberntes后,容器中的Service变得较多,怎样让这么多Service被集群外部的服务所访问也是一个急需解决的问题,NodePort这样一种方案显然不太适合。
那么这里,我们就介绍一个 Ingress 的方式,且搭配TKE所自带提供的Ingress完成服务的外部暴露。
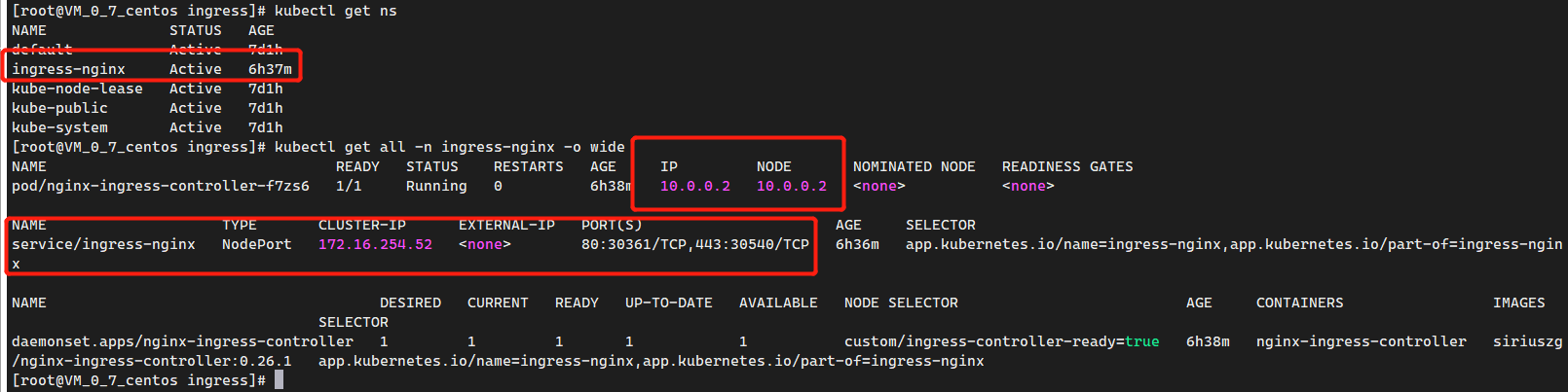
现有环境如下
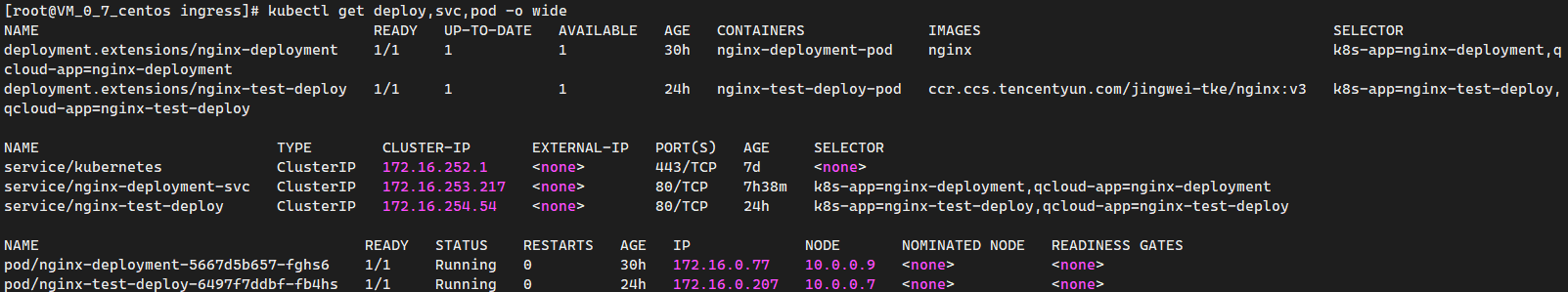
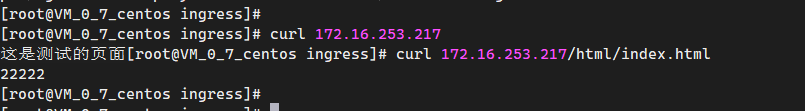
访问 nginx-deploy-svc 服务
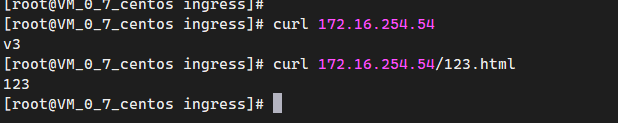
访问 nginx-test-deploy 服务
1、部署 Ingress
由于云服务商所提供的 Ingress 更倾向于LoadBlance 的形式,对一些集群内部的Service支持并不好,所以我们采用自建 Ingress。
GitHub官方项目地址:https://github.com/kubernetes/ingress-nginx ,官方文档地址:https://kubernetes.github.io/ingress-nginx/deploy/
目前文档中一般采用Deployment的方式部署,但是个人比较喜欢通过DaemonSet的形式,并通过Label固定到某台主机上。所以需要对该Deployment文件进行改写。
部署共包含两个文件: mandatory.yaml 以及 service-nodeport.yaml
1.下载所需文件
(可通过GitGub中ingress-nginx项目下deploy,选定需要的版本)
<1>.mandatory.yaml
<2>.service-nodeport.yaml
注意事项:
mandatory.yaml 该文件需要注意的一点是,目前项目组下部署均为Deployment方式,无法做到DaemonSet与Node主机网络相同,\
访问需http://域名:端口(该端口不为80);
如需需网络相同的方式,可以通过修改该文件中Deployment修改为DaemonSet.
实现访问http://域名:端口(端口可省略因默认为80)
详细操作:
1. 修改mandatory.yaml 中 Deployment为DaemonSet;
2. 删除replicas,因为DaemonSet中不包含replicas;
3. 在Spec下添加字段,使pod共享宿主机网络,暴露所监听的端口;
hostNetwork: true
4. 通过指定标签Node部署;
nodeSelector:
custom/ingress-controller-ready: "true"
5. 为需要运行该ingress的节点node添加标签;
kubectl label nodes node01 custom/ingress-controller-ready=true
(如操作错误,label也可通过edit node node01 选择删除)
6. 运用该两个文件;
kubectl apply -f mandatory.yaml
kubectl apply -f service-nodeport.yaml
7. 查看状态;
kubectl get all -n ingress-nginx修改过的 mandatory.yaml
apiVersion: v1
kind: Namespace
metadata:
name: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
kind: ConfigMap
apiVersion: v1
metadata:
name: nginx-configuration
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
kind: ConfigMap
apiVersion: v1
metadata:
name: tcp-services
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
kind: ConfigMap
apiVersion: v1
metadata:
name: udp-services
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRole
metadata:
name: nginx-ingress-clusterrole
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
rules:
- apiGroups:
- ""
resources:
- configmaps
- endpoints
- nodes
- pods
- secrets
verbs:
- list
- watch
- apiGroups:
- ""
resources:
- nodes
verbs:
- get
- apiGroups:
- ""
resources:
- services
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- "extensions"
- "networking.k8s.io"
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- "extensions"
- "networking.k8s.io"
resources:
- ingresses/status
verbs:
- update
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: Role
metadata:
name: nginx-ingress-role
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
rules:
- apiGroups:
- ""
resources:
- configmaps
- pods
- secrets
- namespaces
verbs:
- get
- apiGroups:
- ""
resources:
- configmaps
resourceNames:
# Defaults to "<election-id>-<ingress-class>"
# Here: "<ingress-controller-leader>-<nginx>"
# This has to be adapted if you change either parameter
# when launching the nginx-ingress-controller.
- "ingress-controller-leader-nginx"
verbs:
- get
- update
- apiGroups:
- ""
resources:
- configmaps
verbs:
- create
- apiGroups:
- ""
resources:
- endpoints
verbs:
- get
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: RoleBinding
metadata:
name: nginx-ingress-role-nisa-binding
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: nginx-ingress-role
subjects:
- kind: ServiceAccount
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
---
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: nginx-ingress-clusterrole-nisa-binding
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: nginx-ingress-clusterrole
subjects:
- kind: ServiceAccount
name: nginx-ingress-serviceaccount
namespace: ingress-nginx
---
apiVersion: apps/v1
kind: DaemonSet
metadata:
name: nginx-ingress-controller
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
spec:
selector:
matchLabels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
template:
metadata:
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
annotations:
prometheus.io/port: "10254"
prometheus.io/scrape: "true"
spec:
nodeSelector:
custom/ingress-controller-ready: "true"
hostNetwork: true
# wait up to five minutes for the drain of connections
terminationGracePeriodSeconds: 300
serviceAccountName: nginx-ingress-serviceaccount
containers:
- name: nginx-ingress-controller
image: siriuszg/nginx-ingress-controller:0.26.1
args:
- /nginx-ingress-controller
- --configmap=$(POD_NAMESPACE)/nginx-configuration
- --tcp-services-configmap=$(POD_NAMESPACE)/tcp-services
- --udp-services-configmap=$(POD_NAMESPACE)/udp-services
- --publish-service=$(POD_NAMESPACE)/ingress-nginx
- --annotations-prefix=nginx.ingress.kubernetes.io
securityContext:
allowPrivilegeEscalation: true
capabilities:
drop:
- ALL
add:
- NET_BIND_SERVICE
# www-data -> 33
runAsUser: 33
env:
- name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
- name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
ports:
- name: http
containerPort: 80
protocol: TCP
- name: https
containerPort: 443
protocol: TCP
livenessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
initialDelaySeconds: 10
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 10
readinessProbe:
failureThreshold: 3
httpGet:
path: /healthz
port: 10254
scheme: HTTP
periodSeconds: 10
successThreshold: 1
timeoutSeconds: 10
lifecycle:
preStop:
exec:
command:
- /wait-shutdown
---
apiVersion: v1
kind: LimitRange
metadata:
name: ingress-nginx
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
spec:
limits:
- default:
min:
memory: 90Mi
cpu: 100m
type: Container未修改使用 NodePort方式 service-nodeport.yaml
apiVersion: v1
kind: Service
metadata:
name: ingress-nginx
namespace: ingress-nginx
labels:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
spec:
type: NodePort
ports:
- name: http
port: 80
targetPort: 80
protocol: TCP
- name: https
port: 443
targetPort: 443
protocol: TCP
selector:
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
---<1>、执行两个yaml文件
[root@VM_0_7_centos ingress]# kubectl apply -f mandatory.yaml
namespace/ingress-nginx unchanged
configmap/nginx-configuration unchanged
configmap/tcp-services unchanged
configmap/udp-services unchanged
serviceaccount/nginx-ingress-serviceaccount unchanged
clusterrole.rbac.authorization.k8s.io/nginx-ingress-clusterrole unchanged
role.rbac.authorization.k8s.io/nginx-ingress-role unchanged
rolebinding.rbac.authorization.k8s.io/nginx-ingress-role-nisa-binding unchanged
clusterrolebinding.rbac.authorization.k8s.io/nginx-ingress-clusterrole-nisa-binding unchanged
daemonset.apps/nginx-ingress-controller unchanged
limitrange/ingress-nginx configured
[root@VM_0_7_centos ingress]# kubectl apply -f service-nodeport.yaml
service/ingress-nginx configured
[root@VM_0_7_centos ingress]#<2>、给需要固定的节点打标签
kubectl label nodes 10.0.0.2 custom/ingress-controller-ready=true<3>、查看情况
2、部署具体Ingress代理规则文件
现在情况是这样,其实这个Service用不用都可以,因为pod的IP与Node的IP一致,网络中的其他主机也是可以访问到的了。我们只需将Ingress的域名指向该台Node 10.0.0.2 即可。示例如下:
test-ingress.yaml 内容如下
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: ingress-chat
namespace: default
annotations:
kubernetes.io/ingress.class: "nginx"
kubernetes.io/tls-acme: "true"
nginx.ingress.kubernetes.io/proxy-body-size: 50m
nginx.ingress.kubernetes.io/rewrite-target: /$2
spec:
rules:
- host: myapp.zzz888.com
http:
paths:
- path: /a(/|$)(.*)
backend:
serviceName: nginx-deployment-svc
servicePort: 80
- path: /b(/|$)(.*)
backend:
serviceName: nginx-test-deploy
servicePort: 80由于没买域名,所以通过修改hosts的方式进行测试。

应用后的Ingress如下:

访问测试

3、结合TKE中LoadBlance,面向外网暴露。
更改SVC的访问类型



更改本地Hosts

访问测试