IPSec (Internet Protocol Security) 是一种开放标准的框架结构,用于为IP网络通信提供安全服务,确保数据的机密性、完整性和来源认证。它通常由两个主要部分组成:Authentication Header (AH) 和 Encapsulating Security Payload (ESP),分别负责数据的认证和加密。IPSec VPN 利用这些安全机制,使远程用户或分支办公室能够通过不安全的公共网络(如互联网)安全地访问企业内部网络资源。
华为防火墙配置IPSec VPN的大致步骤如下:
1. 准备工作
- 确定网络拓扑和需求:明确远程站点和总部的网络地址范围、安全要求、认证方式等。
- 收集信息:包括两端的公有IP地址(或动态DNS域名,如果使用动态IP)、预共享密钥(PSK)、认证和加密算法等。
2. 配置IKE(Internet Key Exchange)策略
- 登录华为防火墙的Web管理界面或CLI。
- 创建IKE安全提议,定义加密算法(如AES-256)、哈希算法(如SHA2-256)、DH组(如group14)、认证方法(预共享密钥)等。
- 创建IKE对等体,指定对端的公网IP地址、安全提议、预共享密钥和对等体标识符。
3. 配置IPSec策略
- 创建IPSec安全提议,定义封装模式(传输或隧道模式)、加密算法、认证算法、PFS(完美前向保密)等。
- 设置IPSec策略,关联IKE对等体和安全提议,定义感兴趣流(即需要加密和保护的网络流量)。
4. 配置IPSec IKE策略
- 将之前定义的IKE安全提议和IPSec安全提议绑定在一起,形成一个完整的IPSec IKE策略。
5. 配置NAT穿越(如果需要)
- 启用NAT穿越(NAT-T)功能,允许IPSec流量通过NAT设备。
6. 配置路由
- 如果需要,配置静态路由指向对端网络,确保数据包能够正确转发。
7. 检查与验证
- 在防火墙的状态页面或使用命令行工具检查IPSec SA的状态,确保隧道已建立并处于活跃状态。
- 从客户端或远程网络尝试访问内部资源,验证连接是否正常。
8. 故障排查
- 如果配置后无法建立连接,检查配置细节、网络可达性、防火墙日志等,以定位问题。
二、配置步骤
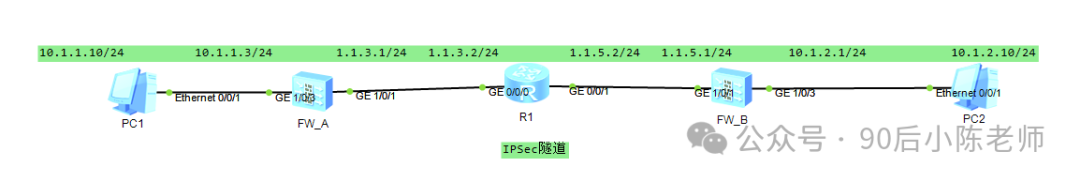
步骤1:防火墙A网络参数
用户名:admin
旧密码:Admin@123
新密码:Huawei@123
(1)接口IP
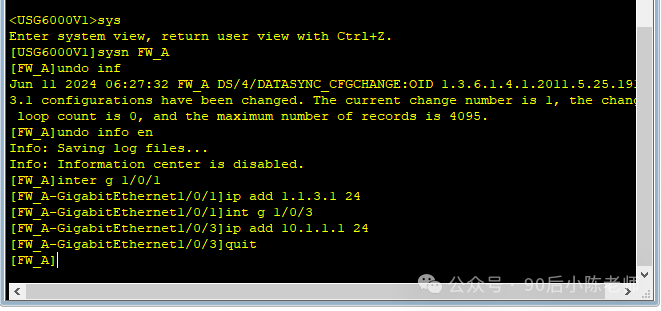
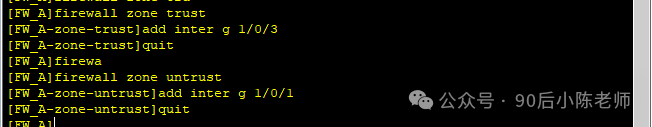
(2)接口加入安全区域
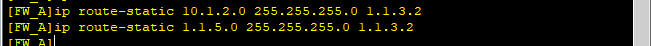
(3)配置到达网络B和隧道对端的路由
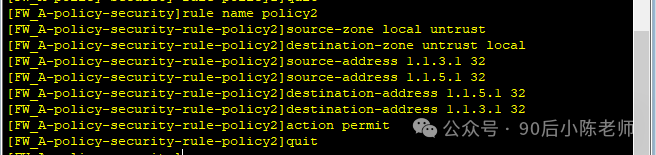
步骤2:防火墙A安全策略
(1)Trust区域和Untrust区域互访
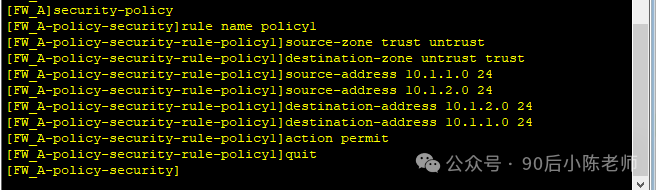
(2)Local区域和Untrust区域互访
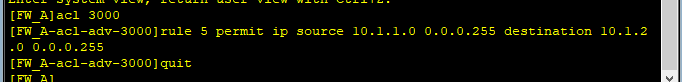
步骤3:防火A配置IPSec
(1)定义被保护的数据流
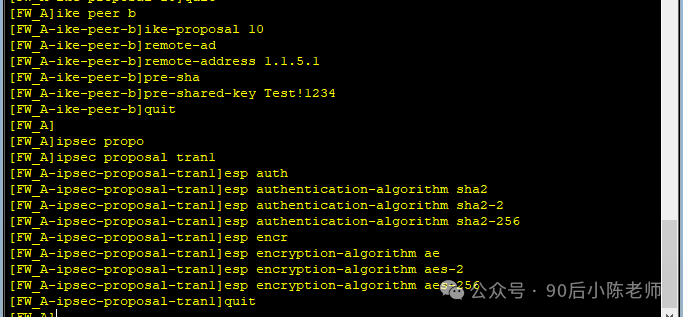
(2)IKE安全提议(防火墙A与B必须相同)
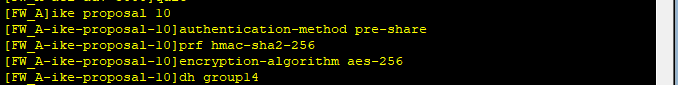
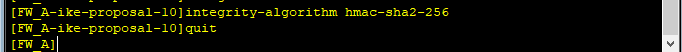
(3)IKE对等体
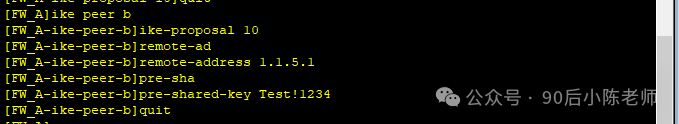
(4)IPSec安全提议(防火墙A与B必须相同)
(5)ISAKMP方式的IPSec
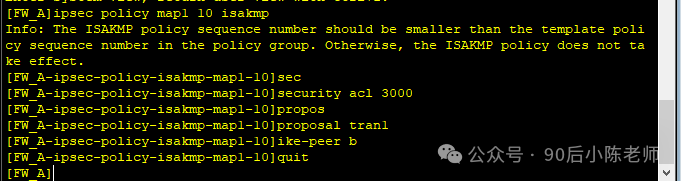
(6)接口上应用IPSec

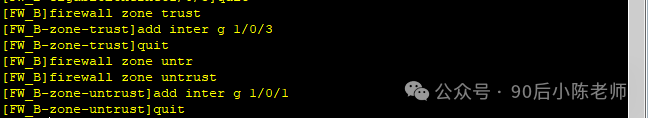
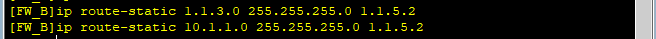
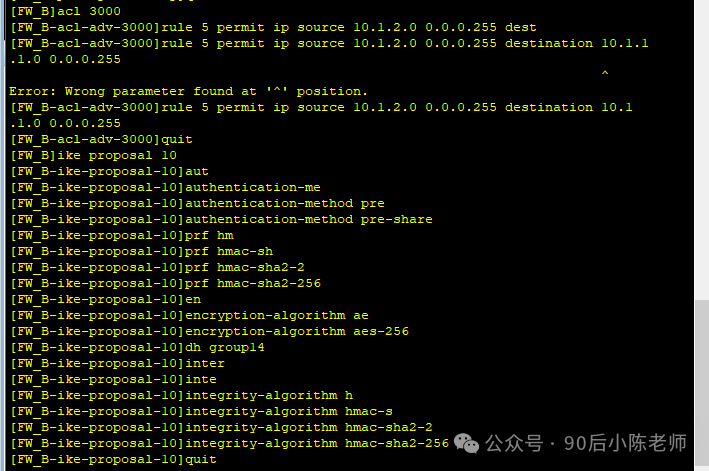
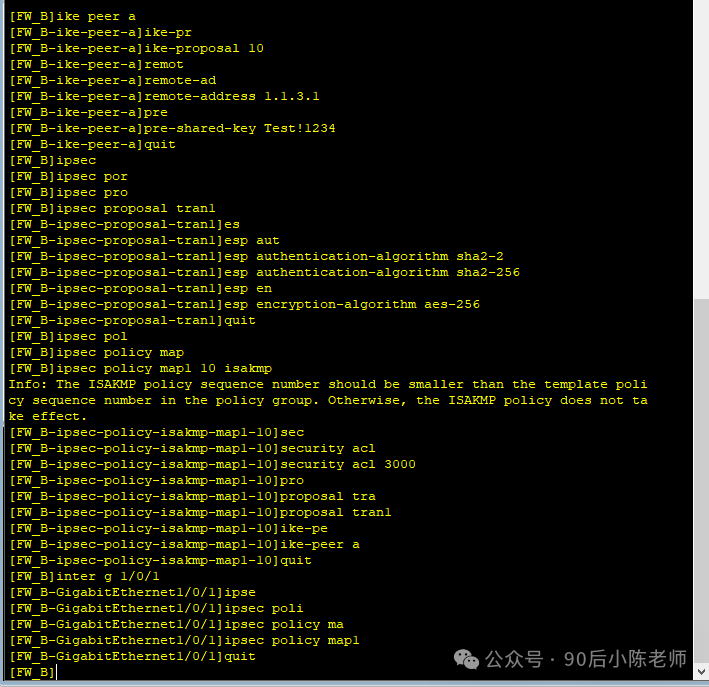
步骤4:配置防火墙B
(1)接口IP
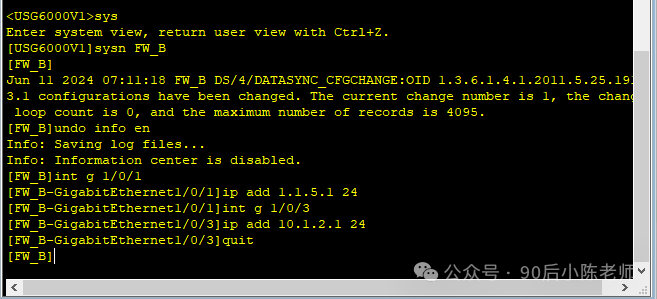
(2)接口加入安全区域
(3)到达网络A和隧道对端的路由
(4)安全策略
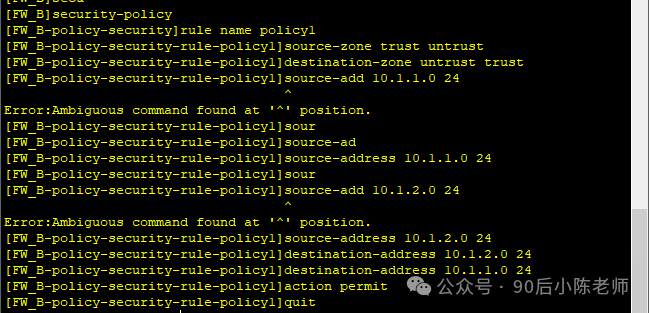
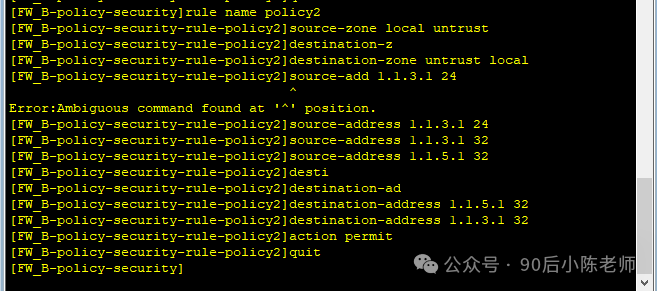
(5)IPSec相关信息
步骤5:其他设备
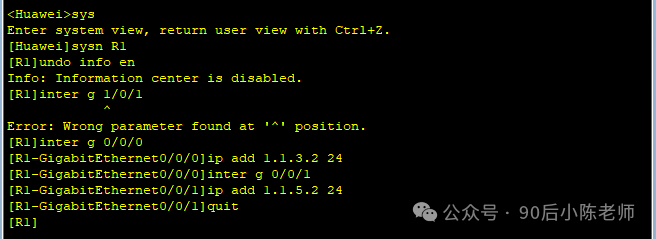
(1)路由器R1
(2)PC1和PC2


步骤6:验证和调试
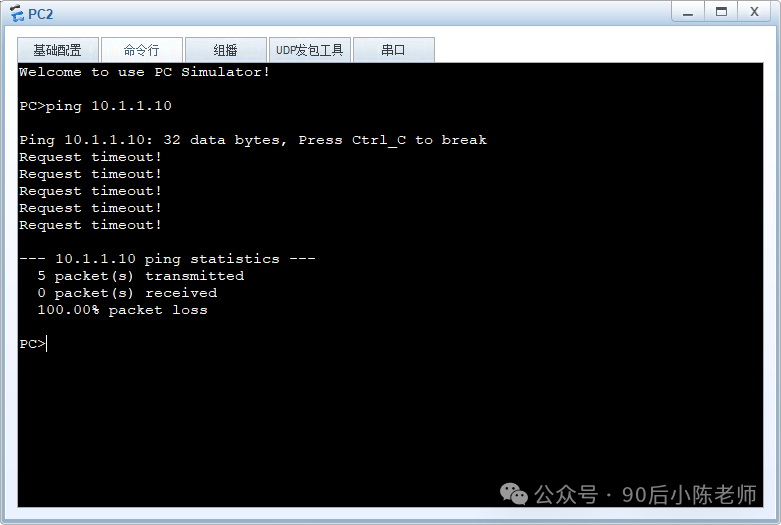
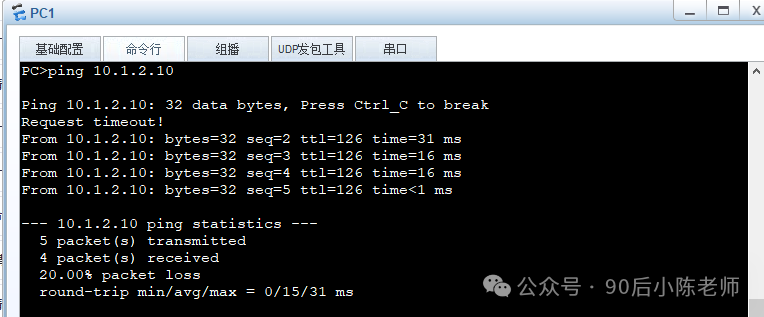
(1)PC1 ping PC2
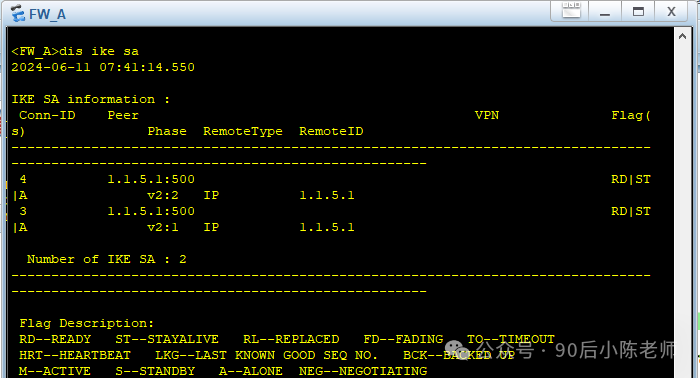
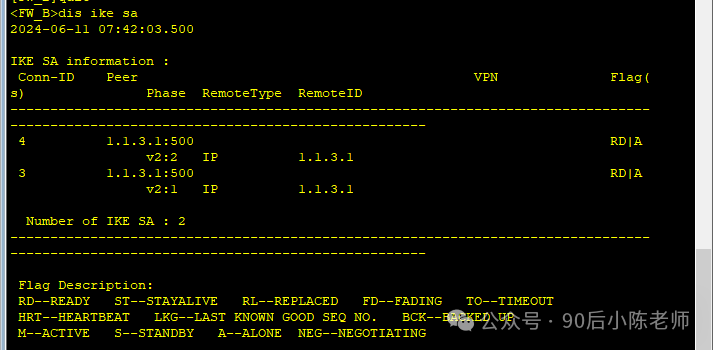
(2)查看IKE SA
防火墙A
防火墙B
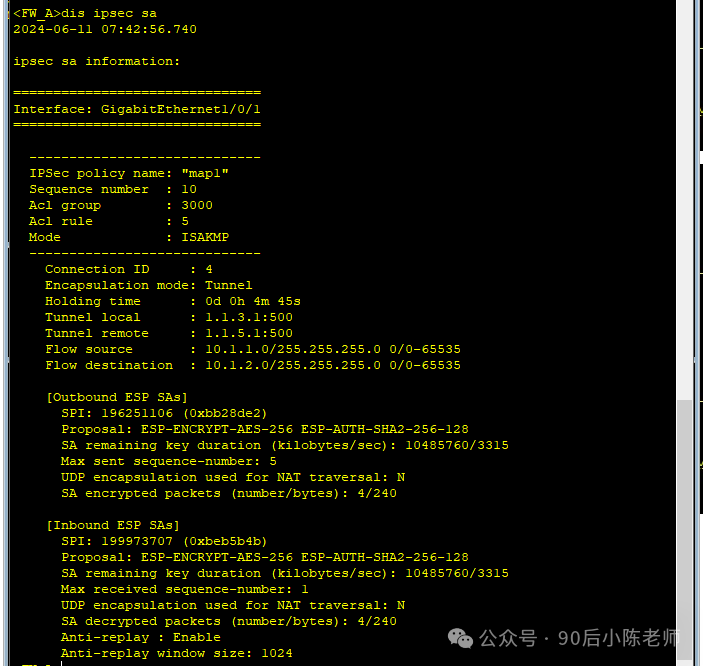
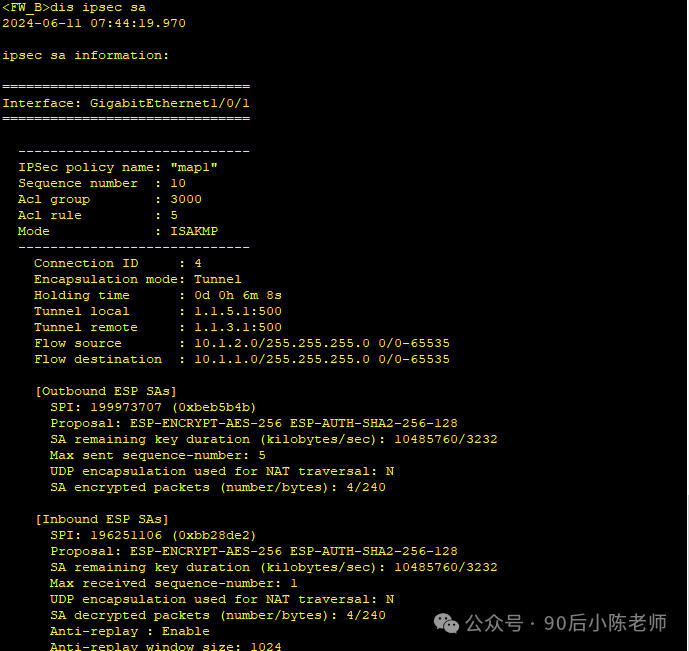
(3)查看IPSec SA
防火墙A
防火墙B
三、完整配置
防火墙A
2024-06-11 07:45:45.660 !Software Version V500R005C10SPC300 # sysname FW_A # l2tp domain suffix-separator @ # undo info-center enable # ipsec sha2 compatible enable # undo telnet server enable undo telnet ipv6 server enable # update schedule location-sdb weekly Sun 00:12 # firewall defend action discard # banner enable # user-manage web-authentication security port 8887 undo privacy-statement english undo privacy-statement chinese page-setting user-manage security version tlsv1.1 tlsv1.2 password-policy level high user-manage single-sign-on ad user-manage single-sign-on tsm user-manage single-sign-on radius user-manage auto-sync online-user # web-manager security version tlsv1.1 tlsv1.2 web-manager enable web-manager security enable # firewall dataplane to manageplane application-apperceive default-action drop # undo ips log merge enable # decoding uri-cache disable # update schedule ips-sdb daily 04:26 update schedule av-sdb daily 04:26 update schedule sa-sdb daily 04:26 update schedule cnc daily 04:26 update schedule file-reputation daily 04:26 # ip vpn-instance default ipv4-family # time-range worktime period-range 08:00:00 to 18:00:00 working-day # acl number 3000 rule 5 permit ip source 10.1.1.0 0.0.0.255 destination 10.1.2.0 0.0.0.255 # ipsec proposal tran1 esp authentication-algorithm sha2-256 esp encryption-algorithm aes-256 # ike proposal default encryption-algorithm aes-256 aes-192 aes-128 dh group14 authentication-algorithm sha2-512 sha2-384 sha2-256 authentication-method pre-share integrity-algorithm hmac-sha2-256 prf hmac-sha2-256 ike proposal 10 encryption-algorithm aes-256 dh group14 authentication-algorithm sha2-256 authentication-method pre-share integrity-algorithm hmac-sha2-256 prf hmac-sha2-256 # ike peer b pre-shared-key %^%#)I56Q}{>TX>W[q'(ETN5x#YiJ`nZ#=YDn{<U(4(=%^%# ike-proposal 10 remote-address 1.1.5.1 # ipsec policy map1 10 isakmp security acl 3000 ike-peer b proposal tran1 # aaa authentication-scheme default authentication-scheme admin_local authentication-scheme admin_radius_local authentication-scheme admin_hwtacacs_local authentication-scheme admin_ad_local authentication-scheme admin_ldap_local authentication-scheme admin_radius authentication-scheme admin_hwtacacs authentication-scheme admin_ad authorization-scheme default accounting-scheme default domain default service-type internetaccess ssl-vpn l2tp ike internet-access mode password reference user current-domain manager-user audit-admin password cipher @%@%aGq_:^(yHPG5l.*(Uw(Pw(jX<x'Q(O$;$7Q0FmB!5(u7(j[w@%@% service-type web terminal level 15manager-user api-admin
password cipher @%@%)YO^2z5%GIb]e8+JJ,o,a>x&%lJJ7.tkmBvY"%'E"2=N>x)a@%@%
level 15manager-user admin
password cipher @%@%+nWr7W6$uC;w=iCvTBY2":,BCM$8>+whi;z_++;F1[9;:,E"@%@%
service-type web terminal
level 15role system-admin
role device-admin
role device-admin(monitor)
role audit-admin
bind manager-user audit-admin role audit-admin
bind manager-user admin role system-adminl2tp-group default-lns
interface GigabitEthernet0/0/0
undo shutdown
ip binding vpn-instance default
ip address 192.168.0.1 255.255.255.0
alias GE0/METHinterface GigabitEthernet1/0/0
undo shutdowninterface GigabitEthernet1/0/1
undo shutdown
ip address 1.1.3.1 255.255.255.0
ipsec policy map1interface GigabitEthernet1/0/2
undo shutdowninterface GigabitEthernet1/0/3
undo shutdown
ip address 10.1.1.1 255.255.255.0interface GigabitEthernet1/0/4
undo shutdowninterface GigabitEthernet1/0/5
undo shutdowninterface GigabitEthernet1/0/6
undo shutdowninterface Virtual-if0
interface NULL0
firewall zone local
set priority 100firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
add interface GigabitEthernet1/0/3firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/1firewall zone dmz
set priority 50ip route-static 1.1.5.0 255.255.255.0 1.1.3.2
ip route-static 10.1.2.0 255.255.255.0 1.1.3.2undo ssh server compatible-ssh1x enable
ssh authentication-type default password
ssh server cipher aes256_ctr aes128_ctr
ssh server hmac sha2_256 sha1
ssh client cipher aes256_ctr aes128_ctr
ssh client hmac sha2_256 sha1firewall detect ftp
user-interface con 0
authentication-mode aaa
user-interface vty 0 4
authentication-mode aaa
protocol inbound ssh
user-interface vty 16 20pki realm default
sa
location
multi-linkif
mode proportion-of-weightright-manager server-group
device-classification
device-group pc
device-group mobile-terminal
device-group undefined-groupuser-manage server-sync tsm
security-policy
rule name policy1
source-zone trust
source-zone untrust
destination-zone trust
destination-zone untrust
source-address 10.1.1.0 mask 255.255.255.0
source-address 10.1.2.0 mask 255.255.255.0
destination-address 10.1.1.0 mask 255.255.255.0
destination-address 10.1.2.0 mask 255.255.255.0
action permit
rule name policy2
source-zone local
source-zone untrust
destination-zone local
destination-zone untrust
source-address 1.1.3.1 mask 255.255.255.255
source-address 1.1.5.1 mask 255.255.255.255
destination-address 1.1.3.1 mask 255.255.255.255
destination-address 1.1.5.1 mask 255.255.255.255
action permitauth-policy
traffic-policy
policy-based-route
nat-policy
quota-policy
pcp-policy
dns-transparent-policy
rightm-policy
return
防火墙B
2024-06-11 07:48:01.760
!Software Version V500R005C10SPC300sysname FW_B
l2tp domain suffix-separator @
undo info-center enable
ipsec sha2 compatible enable
undo telnet server enable
undo telnet ipv6 server enableupdate schedule location-sdb weekly Sun 07:01
firewall defend action discard
banner enable
user-manage web-authentication security port 8887
undo privacy-statement english
undo privacy-statement chinese
page-setting
user-manage security version tlsv1.1 tlsv1.2
password-policy
level high
user-manage single-sign-on ad
user-manage single-sign-on tsm
user-manage single-sign-on radius
user-manage auto-sync online-userweb-manager security version tlsv1.1 tlsv1.2
web-manager enable
web-manager security enablefirewall dataplane to manageplane application-apperceive default-action drop
undo ips log merge enable
decoding uri-cache disable
update schedule ips-sdb daily 04:46
update schedule av-sdb daily 04:46
update schedule sa-sdb daily 04:46
update schedule cnc daily 04:46
update schedule file-reputation daily 04:46ip vpn-instance default
<FW_B>save cu
<FW_B>save cu
^
Error: Wrong parameter found at '^' position.
<FW_B>
<FW_B>dis c
<FW_B>dis current-configuration
2024-06-11 07:48:15.200
!Software Version V500R005C10SPC300sysname FW_B
l2tp domain suffix-separator @
undo info-center enable
ipsec sha2 compatible enable
undo telnet server enable
undo telnet ipv6 server enableupdate schedule location-sdb weekly Sun 07:01
firewall defend action discard
banner enable
user-manage web-authentication security port 8887
undo privacy-statement english
undo privacy-statement chinese
page-setting
user-manage security version tlsv1.1 tlsv1.2
password-policy
level high
user-manage single-sign-on ad
user-manage single-sign-on tsm
user-manage single-sign-on radius
user-manage auto-sync online-userweb-manager security version tlsv1.1 tlsv1.2
web-manager enable
web-manager security enablefirewall dataplane to manageplane application-apperceive default-action drop
undo ips log merge enable
decoding uri-cache disable
update schedule ips-sdb daily 04:46
update schedule av-sdb daily 04:46
update schedule sa-sdb daily 04:46
update schedule cnc daily 04:46
update schedule file-reputation daily 04:46ip vpn-instance default
ipv4-familytime-range worktime
period-range 08:00:00 to 18:00:00 working-dayacl number 3000
rule 5 permit ip source 10.1.2.0 0.0.0.255 destination 10.1.1.0 0.0.0.255ipsec proposal tran1
esp authentication-algorithm sha2-256
esp encryption-algorithm aes-256ike proposal default
encryption-algorithm aes-256 aes-192 aes-128
dh group14
authentication-algorithm sha2-512 sha2-384 sha2-256
authentication-method pre-share
integrity-algorithm hmac-sha2-256
prf hmac-sha2-256
ike proposal 10
encryption-algorithm aes-256
dh group14
authentication-algorithm sha2-256
authentication-method pre-share
integrity-algorithm hmac-sha2-256
prf hmac-sha2-256ike peer a
pre-shared-key %^%#w,}EEs[rK/RlcsABt)~5n#9lOjthnCah}Q,uQ!/E%^%#
ike-proposal 10
remote-address 1.1.3.1ipsec policy map1 10 isakmp
security acl 3000
ike-peer a
proposal tran1aaa
authentication-scheme default
authentication-scheme admin_local
authentication-scheme admin_radius_local
authentication-scheme admin_hwtacacs_local
authentication-scheme admin_ad_local
authentication-scheme admin_ldap_local
authentication-scheme admin_radius
authentication-scheme admin_hwtacacs
authentication-scheme admin_ad
authorization-scheme default
accounting-scheme default
domain default
service-type internetaccess ssl-vpn l2tp ike
internet-access mode password
reference user current-domain
manager-user audit-admin
password cipher @%@%r^Jw!$61n0biZQ<~g[r97M{GZbSD,6(f;%fK7"XQkEBBM{J7@%@%
service-type web terminal
level 15manager-user api-admin
password cipher @%@%fzvx<)h$WTbv&i4&bM(->];7EhiLN.wS>BDn%&J;O0hM];:>@%@%
level 15manager-user admin
password cipher @%@%omb]SfI=d75[z]">~uo14p+T2R2HXp<8n!$9=4*R7#w!p+W4@%@%
service-type web terminal
level 15role system-admin
role device-admin
role device-admin(monitor)
role audit-admin
bind manager-user audit-admin role audit-admin
bind manager-user admin role system-adminl2tp-group default-lns
interface GigabitEthernet0/0/0
undo shutdown
ip binding vpn-instance default
ip address 192.168.0.1 255.255.255.0
alias GE0/METHinterface GigabitEthernet1/0/0
undo shutdowninterface GigabitEthernet1/0/1
undo shutdown
ip address 1.1.5.1 255.255.255.0
ipsec policy map1interface GigabitEthernet1/0/2
undo shutdowninterface GigabitEthernet1/0/3
undo shutdown
ip address 10.1.2.1 255.255.255.0interface GigabitEthernet1/0/4
undo shutdowninterface GigabitEthernet1/0/5
undo shutdowninterface GigabitEthernet1/0/6
undo shutdowninterface Virtual-if0
interface NULL0
firewall zone local
set priority 100firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
add interface GigabitEthernet1/0/3firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/1firewall zone dmz
set priority 50ip route-static 1.1.3.0 255.255.255.0 1.1.3.2
ip route-static 1.1.3.0 255.255.255.0 1.1.5.2
ip route-static 10.1.1.0 255.255.255.0 1.1.3.2
ip route-static 10.1.1.0 255.255.255.0 1.1.5.2undo ssh server compatible-ssh1x enable
ssh authentication-type default password
ssh server cipher aes256_ctr aes128_ctr
ssh server hmac sha2_256 sha1
ssh client cipher aes256_ctr aes128_ctr
ssh client hmac sha2_256 sha1firewall detect ftp
user-interface con 0
authentication-mode aaa
user-interface vty 0 4
authentication-mode aaa
protocol inbound ssh
user-interface vty 16 20pki realm default
sa
location
multi-linkif
mode proportion-of-weightright-manager server-group
device-classification
device-group pc
device-group mobile-terminal
device-group undefined-groupuser-manage server-sync tsm
security-policy
rule name policy1
source-zone trust
source-zone untrust
destination-zone trust
destination-zone untrust
source-address 10.1.1.0 mask 255.255.255.0
source-address 10.1.2.0 mask 255.255.255.0
destination-address 10.1.1.0 mask 255.255.255.0
destination-address 10.1.2.0 mask 255.255.255.0
action permit
rule name policy2
source-zone local
source-zone untrust
destination-zone local
destination-zone untrust
source-address 1.1.3.0 mask 255.255.255.0
source-address 1.1.3.1 mask 255.255.255.255
source-address 1.1.5.1 mask 255.255.255.255
destination-address 1.1.3.1 mask 255.255.255.255
destination-address 1.1.5.1 mask 255.255.255.255
action permitauth-policy
traffic-policy
policy-based-route
nat-policy
quota-policy
pcp-policy
dns-transparent-policy
rightm-policy
return
路由器R1
[V200R003C00]sysname R1
snmp-agent local-engineid 800007DB03000000000000
snmp-agentclock timezone China-Standard-Time minus 08:00:00
portal local-server load portalpage.zip
drop illegal-mac alarm
undo info-center enable
set cpu-usage threshold 80 restore 75
aaa
authentication-scheme default
authorization-scheme default
accounting-scheme default
domain default
domain default_admin
local-user admin password cipher %%K8m.Nt84DZ}e#<0`8bmE3Uw}%%
local-user admin service-type httpfirewall zone Local
priority 15interface Ethernet0/0/0
interface Ethernet0/0/1
interface Ethernet0/0/2
interface Ethernet0/0/3
interface Ethernet0/0/4
interface Ethernet0/0/5
interface Ethernet0/0/6
interface Ethernet0/0/7
interface GigabitEthernet0/0/0
ip address 1.1.3.2 255.255.255.0interface GigabitEthernet0/0/1
ip address 1.1.5.2 255.255.255.0interface NULL0
user-interface con 0
authentication-mode password
user-interface vty 0 4
user-interface vty 16 20wlan ac
return
PC1

PC2